使用 Web Bot Auth(实验性功能)对请求进行身份验证
Google 正在测试 Web Bot Auth IETF 互联网草案的应用。这是一种全新的加密协议,旨在帮助网站验证漫游器是否真实可靠。我们正通过托管在 Google 基础设施上的一些 AI 智能体对该协议进行测试。本指南介绍了 Web Bot Auth 是什么、当前状态,以及如何在实验阶段实现验证。
什么是 Web Bot Auth?
Web Bot Auth 是一种实验性加密协议,用于对漫游器发送的请求进行身份验证。 Web Bot Auth 不再仅仅依赖于自报告的标头和 IP 地址,而是允许智能体对其请求进行加密签名。
使用 Web Bot Auth 有助于网站所有者识别其网站上的自动化流量,并防止其他攻击者企图仿冒信誉良好的智能体。Web Bot Auth 可带来以下好处:
- 加密确定性:告别容易被伪造的标头,转而采用经过验证的身份,并实现智能体身份与 IP 地址的解耦。
- 提升可观测性:更深入地洞察智能体与您的内容进行互动的具体情况。
- 前瞻性布局:助力构建一个让智能体提供商与网站能够建立互信,并做出明智访问决策的网络环境。
Web Bot Auth 的当前状态:实验性
Google 的 Web Bot Auth 实现目前处于实验阶段,原因如下:
- Web Bot Auth 目前是由 IETF WBA 工作组制定的规范草案,未来可能会有所变动。Google 将随着该工作组的不断演进,持续深度参与其相关工作。
- 基于 User-Agent 和 IP 地址的漫游器验证是目前行业内事实上的标准,数十年来,无数的系统、政策和最佳实践均是围绕这一标准构建而成的。改变这些现状并非一朝一夕之功,需要审慎推进。我们目前尚处于早期阶段,仍在评估该协议的技术特性及其对生态系统可能产生的深远影响。
这是什么意思?
实验性状态表示:
- 并非所有 Google 用户代理都使用 Web Bot Auth。
- Google 尚未对使用该协议的智能体所发出的每一项请求进行签名。
- 在逐步推行签名流量的过程中,我们建议您在采用 Web Bot Auth 的同时,继续沿用 IP 地址、反向 DNS 和 User-Agent 字符串进行验证。
对于有兴趣在实验阶段参与体验的用户,我们将提供相关指南,帮助您识别 Google AI 智能体并将其列入许可名单。
如何使用 Web Bot Auth 将 Google AI 智能体列入许可名单
如果您是开发者或系统管理员,并希望将我们的实验性 AI 智能体列入许可名单,则可以通过 Web Bot Auth 协议实现验证:
使用支持 Web Bot Auth 的产品或服务
主流的漫游器检测服务、CDN 和 WAF 均支持 Web Bot Auth。部分基础设施服务提供了识别 Google-Agent 用户代理并将其列入许可名单的方法;具体操作步骤请咨询您的服务提供商。Google-Agent 发出的一部分请求使用 Web Bot Auth 进行签名;在这些情况下,这些请求的身份验证结果为 https://agent.bot.goog。如果您的提供商支持该协议,他们可能会自动验证这一点。
自行验证请求
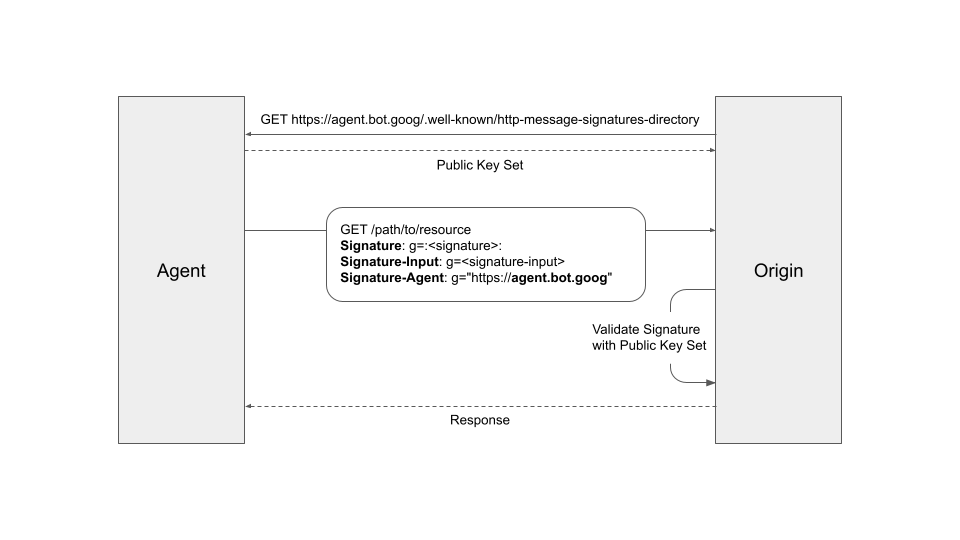
如果您想自行验证我们的请求,请参阅《自动化流量架构规范:HTTP 消息签名》以及 GitHub 上的示例实现。一般来说,关键协议步骤如下:
- 从 https://agent.bot.goog/.well-known/http-message-signatures-directory 中提取智能体的公钥集,并根据
Cache-Control标头缓存这些公钥。 - 发送到您服务器的参与请求会将
Signature-AgentHTTP 请求标头设为g="https://agent.bot.goog"(请留意g=标签)。 - 根据
Signature-Input验证Signature标头,遵循 HTTP 消息签名标准 (RFC 9421)。 使用标记为g的Signature和Signature-Input标头。 - 请务必配合使用基于 IP 的验证作为回退方案,因为并非所有请求都带有签名。
对于对延迟敏感的请求,您可以提前返回响应,然后在有效期内验证签名。在这种情况下,处置操作将在事后执行,您可以将处理结果应用于该调用方后续发出的请求。
后续步骤
- 请咨询您的托管或安全服务提供商,确认其是否支持 Web Bot Auth 验证。
- 关注 Web Bot Auth 工作组 的最新技术规范。
- 在 IETF 论坛上参与讨论。
- 通过 Web Bot Auth 反馈表单向我们发送反馈。